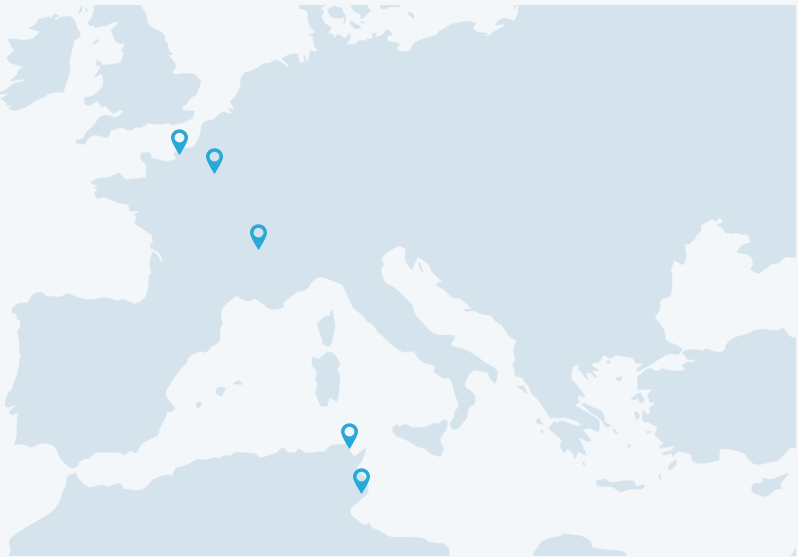
Nous avons su étendre notre présence de part et d’autre de la Méditerranée, faisant ainsi de cette mer légendaire, un véritable pont au service de nos clients. Avec des bureaux solidement ancrés sur les côtes nord et sud, NUMERYX la société de service it incarne la rencontre harmonieuse de l’Orient et de l’Occident, du savoir faire technologique et de l’expertise de pointe.
Notre portefeuille d’experts au service de votre entreprise.
Cybersécurité, Conseil & Intégration, IT & Software Services, Infrastructure, Sécurité réseaux & cloud, Systèmes Industriels & Embarqués